December 2023
- Minor security enhancements and fixes.
November 2023
Enhancements
-
MFP configuration for network keys.
-
6 GHz support is now available in test profile templates and template elements.
Issues Resolved
-
Fixes Eye connection fails on first start up due to default route missing.
- Messages have been sent to customers who may still have Sapphire Eyes in their boxes. If you received a Sapphire Eye(s) before October 20th and are encountering connection issues during setup, kindly submit a support ticket, and we'll be happy to assist you.
- Fixes an issue where user tries move to Map view from Network Alarms view. The "Map" option was not available for users in most of the cases.
- Fixes issue when user is trying to change his/her password in Configurator, the UI locks up.
October 2023
Enhancements
- Introduces the ability to lock in network and band selections in the topology pane.
- SSH service is now disabled by default on Eyes. Users can enable the service on a per-Eye basis if required. Note that if the Eye's SSH password remains as the default, users will be prompted to change it first.
- Enhances SLA tables by including Related KPIs data for new high-level KPIs (HC001-004). Related KPIs encompass the sub-KPIs associated with these high-level KPIs.
- Improved logging for sensors automatically removed due to inactivity:
- Enhanced log message now includes organization name, service area, Eye Ethernet MAC address, and IP address for easier sensor identification.
- Introducing a system alarm for inactivity-related Eye removal, including service area, Eye Ethernet MAC, and IP address details.
- Auditing messages are sent to the platform audit service.
This update includes additional fields in the log message and introduces a new system alarm called "Eye remove due to disconnect period."
Issues Resolved
- Eye 250 now includes support for starting and stopping SSHD service.
- In utilization tests, after transitioning to JSON format for test results, channel utilization values are now correctly populated in the test result Java classes.
September 2023
Enhancements
- In anticipation of the upcoming release of our latest Sapphire Eye device early next year, we're thrilled to announce enhanced support for the 6 GHz frequency band in Analyzer and Configurator.
- Notify users to change their SSH passwords. See Tech Notes for additional information Notify Users to Change the Default SSH Password (7signal.com).
- New skin/color palette for Configurator - We are in the process of aligning our product's appearance with our branding.
Security Enhancements
- Cross Site Swagger-UI Scripting vulnerability in the API documentation for Sapphire.
- Open redirect vulnerability in IQ for Sapphire.
Issues Resolved
- Under certain conditions, automated reports were only showing one network.
- Display issue, VoIP packet loss percentage > 1,000%.
- DHCP test reporting when testing on Ethernet.
August 2023
- SLA threshold changes for Dashboard report. The following KPI bars will stay green until 95% and stay yellow until 90% - Connectivity, Authentication, IP and DNS Services, Quality.
- 802.1X Ethernet authentication testing added
- Support for 6 GHz in Analyzer reports and automated reports (Configurator)
- Additional security enhancements and fixes
July 2023
-
Security enhancements
-
Additional support for 6GHz (Sapphire Eye 6300)
-
Allow redirector to use ports 80 and 443, in addition to port 53
-
Prevent log files from filling up disk space
February 2023
- Various bug fixes, usability enhancements and user interface improvements
- Additional support for Wi-Fi 6 and the Sapphire Eye 6200
January 2023
- Restrictions placed on the length of reports that may be run in Analyzer to improve performance.
| History | Averages | |||
| 1 hour | 1 minute | 10 minutes | 1 hour | |
| 6 hours | 1 minute | 10 minutes | 1 hour | |
| 1 day | 1 minute | 10 minutes | 1 hour | 1 day |
| 2 days | 10 minutes | 1 hour | 1 day | |
| 1 week | 10 minutes | 1 hour | 1 day | |
| 1 month | 1 hour | 1 day | ||
| 3 months | 1 day | |||
December 2022
- New key performance indicators, available on the SLA and End to End reports:
- Ping Gateway Success Rate
- Ping Gateway RTT (round trip time)
- Ping Gateway alarms also added.
- Filter by band on the Best/Worst report
November 2022
- Additional support for Wi-Fi 6 (802.11ax)
- Automated reports may now be delivered in .csv format (SLA and KPI reports)
- Channel notation change that identifies an AP's primary channel and channel width (for example "36, 80 MHz")
October 2022
- Additional support for Wi-Fi 6 (802.11ax) and continued development on Sapphire Eye 6200
- Simple cosmetic changes to Configurator
- Business hours filter may now be applied when configuring automated reports
September 2022
Various bug fixes and minor enhancements, including...
Analyzer
- Dashboard - small charts fixed
- Spectrum - data now displayed for channels 165 and 169
- All reports will display the KPI Name, not the internal ID
Configurator
- Specify an alarm for a specific endpoint
- EAP certificates verified upon upload
August 2022
Analyzer
- Data Rates - 7MCS and MCS Wi-Fi quality scores now available for clients
- Frames - client reports will now only show KPIs relevant to clients
- All reports will display the KPI Name, not the internal ID
- Dashboard - the Worst AP's list now shows AP names
- Various bug fixes and small enhancements
- Persistent LLDP/CDP information now available
- Ability to choose the network key in a manual test
- Manage automated tests from location or service area perspective
- "7config conn check" utility now checks TLS connection in addition to TCP
June 2022
-
Usability Improvement - locations and service areas listed in alphabetical order
-
Wi-Fi 6 KPI Support
-
In BSSID Info - inspect the MU-EDCA parameters to understand how your AP's are favoring OFDMA transmissions for Wi-Fi 6 (802.11ax ) clients.
-
May 2022
- Sonar Server - Please upgrade to the latest version to get important bug fixes and performance enhancements. Upgrade instructions may be found at the bottom of this page. If you need assistance, please contact Customer Support.
- Security Enhancements - Support for WPA3 Enterprise
- Usability Improvements - Locations with no service areas are now hidden in Analyzer topology
- Wi-Fi 6 KPI Support - 802.11ax frames now included in the following calculations:
- Total Client Retries
- (Total MU client retries) / (SU filtered frame total + MU frame total) = Combined retry rate
- Single-user AP Retries
- Single-user Client Retries - client retries that occur with any single user modulation in any supported PHY can be counted directly using the retry bit in the MAC header
- Multi-user Client Retries - client retries that occur within OFDMA can be inferred from examining the Mult-STA BlockAck frame that follows UL OFDMA
- Total Airtime Utilization % (now includes all frames all PHYs)
- OFDMA Airtime Utilization % (does not include DL OFDMA)
- UL OFDMA Airtime Utilization %
- OFDMA traffic Volume % (also does not include DL OFDMA)
- BSS Info (Configurator and Analyzer information dialogs)
- Spatial Reuse Parameters
- AP Channel Report
- Reduced Neighbor Report
- AP Change Events for BSS Color Changes
- Total Client Retries
April 2022
- Support for OWE (Opportunistic Wireless Encryption for open networks)
- Replaced 7SIGNAL's internal AP identifier with AP Name from the following Analyzer reports: SLA, End-to-End, Frames, Channels, and Data Rates
April 2022 Security Notification Regarding Spring4Shell
- Document download
-
Date and time incident began: April 8, 2022
Date and time incident ended: April 14, 2022 (planned at time of issued document) -
Published Vulnerability:
A Spring MVC or Spring WebFlux application running on JDK 9+ may be vulnerable to
remote code execution (RCE) via data binding. The specific exploit requires the
application to run on Tomcat as a WAR deployment. If the application is deployed as a
Spring Boot executable jar, i.e. the default, it is not vulnerable to the exploit. However,
the nature of the vulnerability is more general, and there may be other ways to exploit
it. -
Impact identified vulnerability:
• Sapphire Eye using version 4.3.2 no impact or risk.
• Sapphire Eye hardware not using Spring Framework.
• Mobile Eye web application not using Spring Framework.
• Mobile Eye Agents Using 5.2.3 (no risk not a web server).
• Production System tested for all Spring Framework products with no risks
identified.
• SIEM logs showed no signs of exploitation. -
Resolution:
• Sapphire Eye will update to a more current version in Q2 or Q3 2022 as planned
in the technical roadmap.
• Mobile Eye Agent will upgrade to 5.3.18 by 4/15/2022 once tested to ensure no
new issues are introduced into Production.
• Mobile Eye Agent.
• No loss of data.
• No security breach or risk was introduced. -
Procedural or Design changes planned:
• Continue to run vulnerability testing with 3rd party tools (per 7SIGNAL policy).
• Continue to monitor https://nvd.nist.gov/vuln/detail/cve-2022-22965 for future
update.
• Reviewed Incident with 7SIGNAL CTO
March 2022
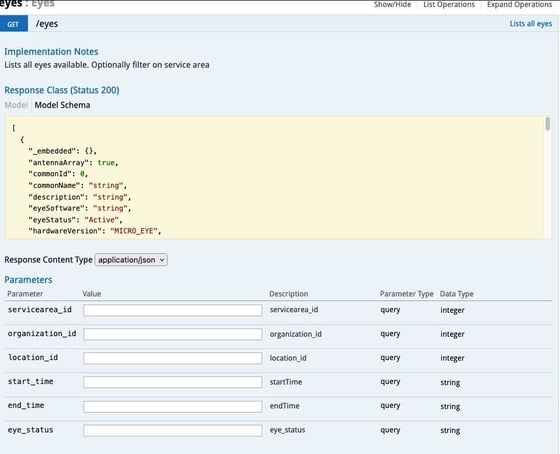
API Enhancements
- GET Sapphire Eye status (idle, active, offline, maintenance)
- GET non-managed access point list
- New function calls visible through online Swagger document
Security Enhancements and Support
- WPA3 and OWE
Usability Improvements
- Analyzer: New URL (region.cloud.7signal.com/analyzer)
- Analyzer: New icons that more accurately depict endpoint destinations (Sonar, web download, ping)
- Analyzer: Show/hide legend available for each chart generated
- Analyzer: Channels report, AP's listed in alpha/numeric order
- Configurator: Map Config, "All Services Areas" is now unselected by default
- Configurator: Date/time stamp provided for when test profile was last updated
- Configurator: For organizations managing multiple tenants, organization list now alphabetized
- Configurator: New system alert for "Webhook Call Failed"
- Support for LLDP upon Sapphire Eye reboot (information discovered is also available through the API)
February 2022
- Various bug fixes and performance improvements.
- Support for IPv6 configuration on testing interfaces, including:
- DHCPv6 KPIs
- SLAAC KPIs
- "Basic" KPI list is changing to reflect the most often used KPIs for the End-to-End and Frames tabs in Sapphire Analyzer.
- End to End Basic KPI List
- Beacon Availability
- Radio Attach Success Rate
- Total EAP Authentication Success Rate
- DHCP Success Rate
- Ping Success Rate
- Ping RTT
- HTTP DL Throughput
- HTTP UL Throughput
- VoIP MOS Download
- VoIP MOS Upload
- Packet Loss
- Jitter
- Signal Strength
- AP Channel
- Frames Basic KPI List
- AP Retries
- Client Retries
- Airtime Utilization
- QBSS Channel Utilization
- Number of Clients per AP
- QBSS Station Count
- End to End Basic KPI List
January 2022 Security Notification Regarding Log4j
-
Log4j update to version 2.17.1 to be applied for all cloud servers in response to Log4j vulnerability CVE-2021-44832.
-
Please update your local Sonar/Carat servers following the instructions towards the bottom of this knowledge base article.
-
Please email Customer Support with any questions.
-
Also as part of this maintenance, fixed the issue with DSCP tagging on uplink for voice and video testing.
December 2021 Security Notification Regarding Log4j
7SIGNAL cloud servers have all been patched and protected from the Log4j vulnerabilities:
CVE-2021-45046
CVE-2021-44228
If you have a Sonar™ server or Sapphire Carat™ server onsite, instructions may be found towards the bottom of this knowledge article. Please contact 7SIGNAL Customer Support if you have questions or need any assistance. Mobile Eye® is not affected by this vulnerability.
November 2021 Release 8.2.3.1
Various bug fixes and improvements including a correction to the Airtime Utilization calculation that occasionally resulted in values greater than 100%. Also, improved Aerohive/Mikrotik/Extreme access point name detection.
August 2021 Release 8.2.3.0
Improved Topology pane makes Analyzer™ reporting easier to use and understand, with new nomenclature, powerful search, and simple checkboxes for filtering.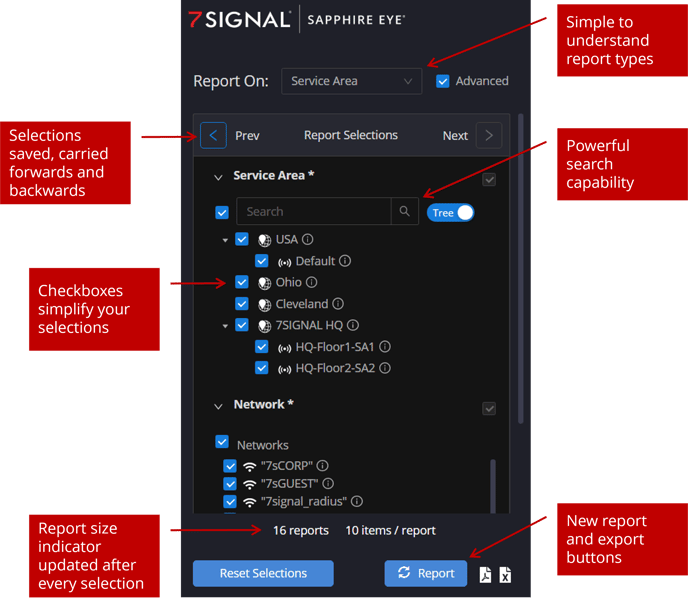
Click here to watch a video...
Table of aggregation name changes below:
| Previous Name | New Name | Description of Aggregation (grouping) |
| NWBandServ | Service Area | Network per band per service area aggregation |
| APEye | Access Point | Access point per Sapphire Eye aggregation |
| APGroup | Access Point Group | Access point group aggregation |
| NW | Network | Network (SSID) aggregation |
| n/a | Location | Location aggregation - NEW TO ANALYZER |
| EyeEth | Eye Ethernet | Sapphire Eye aggregation, Ethernet testing |
| EyeAnt | Eye Antenna | Sapphire Eye antenna aggregation |
| Eye | Eye Wi-Fi | Sapphire Eye aggregation |
| ChEye | Channel | Sapphire Eye channel aggregation |
| DestAP | Destination | Sonar endpoint per access point aggregation |
- Less common aggregations now hidden by default. Check the Advanced box at the top of the pane to reveal.
- The following aggregations have been deprecated...
- DestEyeEth, Link, NWServ, NWEye, NWBand, NWBandServ, NWBandEye, NWBandEyeAnt, APEyeAnt, ChEyeAnt, QoSAP
- Only selections that are relevant to the report at-hand are displayed.
- Use new search functionality to find anything (Service Area, AP, Network, etc.)
- Selections are saved and carried forward to the next report tab. You may also go back to a previous set of selections.
- An additional 'generate report' button has been added to the bottom of the Topology pane, along with PDF and CSV export icons.
- Report size indicator updates after each Topology selection and appears at the bottom of the Topology pane.
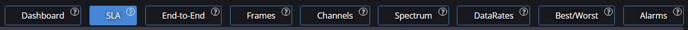
New top navigation menu - reordered to accommodate the most common troubleshooting workflows.
July 2021 Release 8.2.2.8
- Meraki access point name identification
- SSID names appear on automated reports
- Ability to pipe packet capture data directly from a Sapphire Eye to a network drive
- Various bug fixes and security enhancements
April 2020 Release 8.2.2
Public Key Infrastructure (PKI) Improvements
- Support for new 7SIGNAL certificate (Eye’s must have this installed prior to May 14 to maintain connectivity to Cloud)
- Improved software signing capabilities
Other Enhancements
- Easier to complete Eye software upgrades
- Disconnected Eye status included in upgrade workflow – tells you what you need to get connected
- Paused test status indicators for Eyes
- OTA Mode Enhancements
- Connection state notifications
- Countdown timer for reconnection to server
- Set test cycle durations
- Supplicant output for WPA
- Ability to disable alarm groups or individual alarms within a group
- Automated Reports – ability to change order of SLA appearance
- AP Naming – option to keep your AP name (and other manual edits) the same even if it is changed on the controller
- DHCP Discover messages KPI added (helps identify Cisco bug)
- Simplified command for showing system logs when SSHd into different Eye models
June 2019 Release 8.2
Sapphire Eye 2200
- Support for 802.11ac Wave 2
Deployment
- RPM based software installations and upgrades improves speed and simplicity of deployment. Use commands below:
- Cloudsmith repository for devops
- #yum install 7signal-Sapphire
- #yum upgrade
Analyzer
- Overall report generation performance improvements
- Data Rates reports now show spatial streams, channel width, mcs, and 802.11 standard in use
- Topology pane now shows disconnected Eyes
- Macro KPIs (EyeQ) now available in Dashboard KPI dropdown selector
- Alarms that are 30 days old now automatically purged
Configurator
- Setup Wizard improvements
- Will simultaneous setup 100 Eyes
- Configurable signal strength and band setup wizard
- LAN test now included
- Automated Reports
- Select the KPI’s you want to see in the SLA report
- Select time intervals
- Use random MAC address
- Configure multiple APs at once with new multi-select feature
- Various bug fixes
Other
- Control over Sapphire Eye LED (blink/no blink/off)
- REST API now supports all KPIs